Stop threats before they reach your business.
Security isn't a roadblock — it's your competitive advantage. Firewall, VPN, automated backups, and full penetration testing to future-proof your infrastructure.
Trusted by the world's most innovative teams


The Security Risk
Most breaches happen to businesses that thought they were "secure enough."
Three threats that are quietly exposing your infrastructure right now.
Unfiltered traffic = open door
The problem
Without a dedicated firewall, every open port is an invitation. Bots scan your IP range 24/7 — and eventually they find something.
Our fix
A properly configured firewall blocks 90–99% of attacks before they reach your servers. One rule set, total peace of mind.
Remote access without VPN = credential theft
The problem
RDP and SSH exposed to the internet are the #1 entry point for ransomware. One leaked password and your entire infrastructure is compromised.
Our fix
VPN authentication means only verified users and devices access your internal resources — exposed ports become invisible to attackers.
No backups = permanent loss
The problem
Ransomware encrypts your data and demands payment. Without tested backups, you either pay or lose everything. Most companies discover this too late.
Our fix
Automated backups to CAS storage. Versioned, encrypted, and recoverable in minutes — not days.
Your Security Foundation
Three layers every infrastructure needs.
Block 99% of attacks at the gate
A dedicated firewall stops unauthorized traffic before it reaches your servers. SSL management, geo restrictions, and traffic monitoring included.
Make your network invisible
VPN authentication hides your internal resources from the public internet. Only verified users and devices get in — everyone else sees nothing.
Recover in minutes, not weeks
Automated backups to CAS mean you can restore any server, any config, any file — even after a ransomware attack.
Enterprise
security assessment.
For organizations with complex IT ecosystems, we provide rigorous penetration testing. A strategic 3-step process designed for annual or quarterly resilience.
White Box
Full transparency. Our testers analyze internal structures, source code, and architecture to simulate insider threats and uncover deep-rooted logic vulnerabilities.
Gray Box
The balanced approach. Testers operate with partial knowledge and limited documentation, combining external perspective with technical insights.
Black Box
True outsider simulation. No prior knowledge of systems or code. We attack from the outside to identify what is visible and exploitable to hackers.
Cyber Security Suite
Deploy security tools instantly
Professional cyber security products from our marketplace. Deploy in minutes, monitor in real-time, and scale your protection as you grow.
How It Works
Fully secured infrastructure in three steps.
No dedicated security team required. Follow this sequence and sleep better tonight.
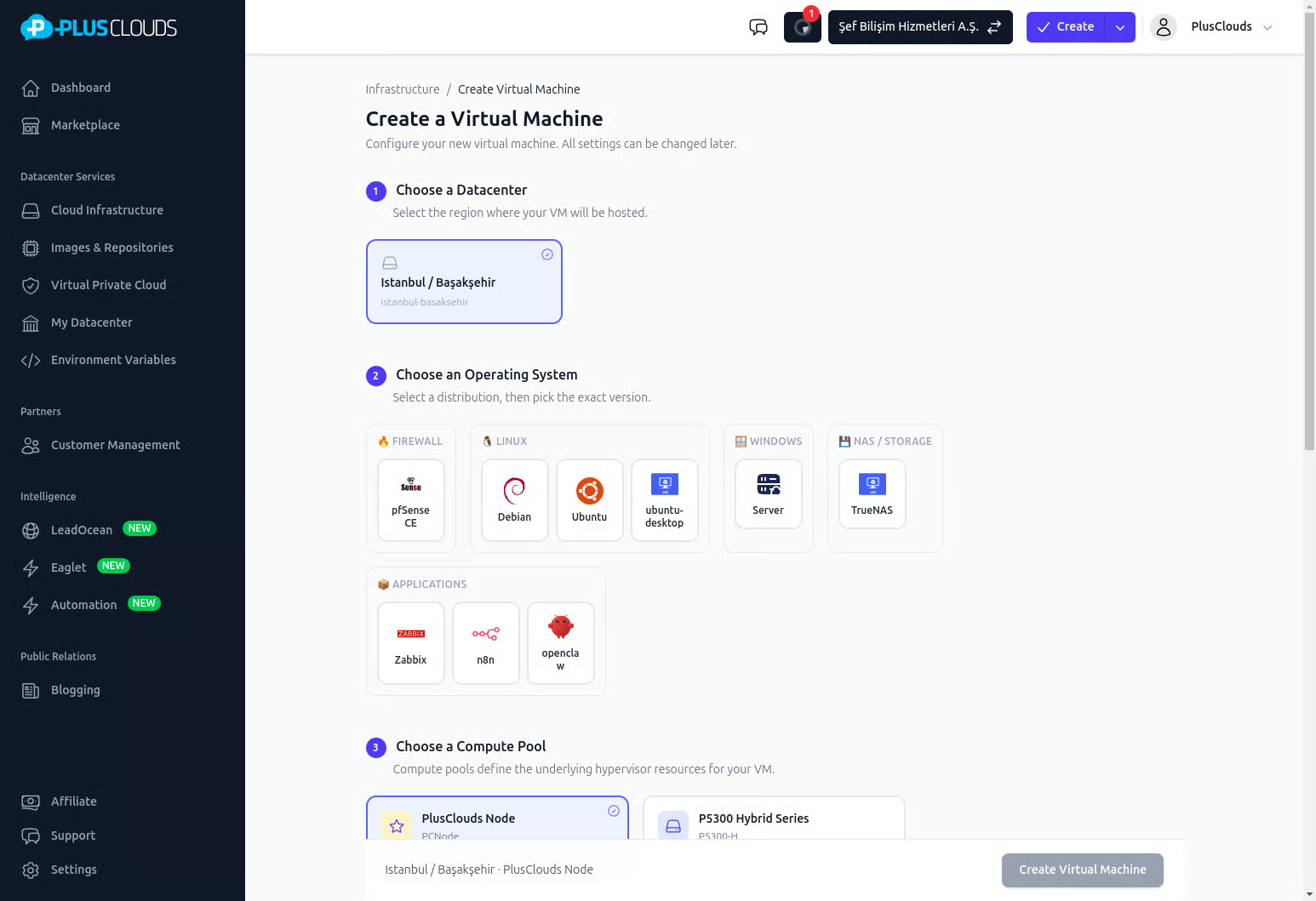
Create your Virtual Datacenter & firewall
One click creates an isolated private network with a dedicated firewall. Your servers are invisible to the public internet from day one.
Deploy & connect your resources
Add servers, databases, and applications inside your secured network. Configure VPN access for your team — external connections require authentication.
Automate backups & run security checks
Schedule automated backups to CAS and subscribe to monthly penetration tests. Your security posture improves continuously, with zero manual effort.
Need a custom security architecture?
Complex compliance requirements, enterprise pentest, or a full security audit? Let's schedule a 20-minute call and design your protection layer.
Frequently asked questions about PlusClouds Security
Still have questions?
For purchases and detailed information, schedule a meeting — or reach us directly:
Get started for free
Deploy your first cloud server in minutes. No credit card required to explore.